
Architecting Secure Access for the Modern Enterprise
30 Apr 2026
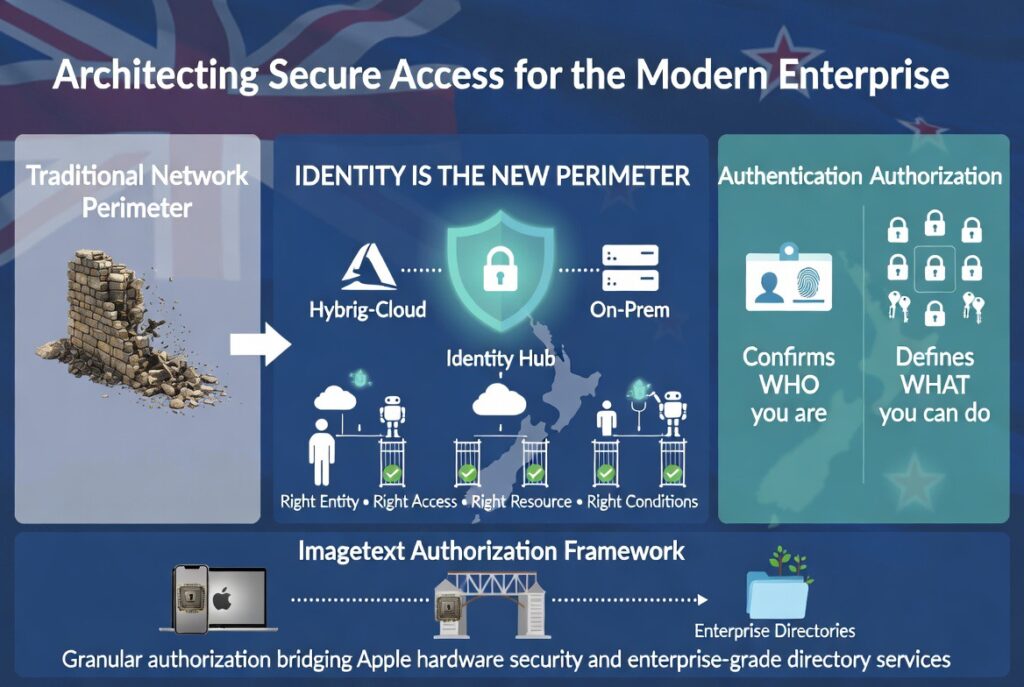
In the contemporary threat landscape, the traditional network perimeter has dissolved. For New Zealand enterprises operating in hybrid-cloud environments, (Identity is the new perimeter). Imagetext Infrastructure Authorization services provide the framework required to ensure that the right entities-human or machine-have the right access to the right resources, under the right conditions.
The Imagetext Authorization Framework: Beyond Authentication
While authentication confirms (who) a user is, (Authorization) defines (what) they can do.
Imagetext specializes in engineering granular authorization protocols that bridge the gap between Apple’s sophisticated hardware security and enterprise-grade directory services.
Our approach integrates Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC) to create a dynamic, context-aware security posture.
1. Zero Trust Network Access (ZTNA) Integration
Imagetext moves organizations away from “trust but verify” to a (Zero Trust) model. Our authorization architectures are built on the principle of explicit verification. We leverage telemetry from endpoints (macOS, iOS, and Windows) to inform authorization decisions in real-time.
• Contextual Signals: Authorization is granted based on device health, geographic location, and risk scores.
• Micro-segmentation: Limiting lateral movement by enforcing authorization at the application and resource level, rather than the network level.
2. Modern Identity Orchestration (Apple & Microsoft Entra ID)
As New Zealand’s premier Apple systems integrator, Imagetext excels at harmonizing Apple hardware with Microsoft Entra ID and Okta environments.
• Jamf Connect & Platform SSO: We implement advanced authorization workflows that allow macOS devices to utilize cloud-native credentials for local account permissions, ensuring a seamless, secure “Single Sign-On” experience that respects enterprise security policies.
• Just-in-Time (JIT) Administration: We deploy solutions that eliminate permanent local admin rights. Using JIT authorization, elevated privileges are granted only when necessary and revoked automatically, drastically reducing the attack surface.
3. Identity Governance and Administration (IGA)
Authorization is not a static event; it is a lifecycle. Imagetext provides the tools and strategic oversight to manage the (Joiner, Mover, Leaver (JML)) process with precision.
• Provisioning & Deprovisioning: Automated authorization workflows ensure that when an employee’s role changes or they leave the organization, access to proprietary infrastructure is updated or severed instantaneously.
• Privileged Access Management (PAM): For high-value infrastructure, we implement hardened authorization gates, requiring multi-factor authentication (MFA) and request-approval chains for any administrative action.
4. Compliance and NZISM Alignment
For our public sector and enterprise clients, infrastructure authorization must align with the (New Zealand Information Security Manual (NZISM) and PSR requirements. Imagetext ensures that your authorization logs are immutable, auditable, and provide the necessary visibility for compliance reporting.
• Least Privilege Enforcement: Every user and service operates with the minimum level of access required, a core requirement for ISO27001 and NZISM compliance.
• Audit Trails: Detailed logging of authorization successes and failures to facilitate rapid incident response and forensic analysis.
Engineering Resilient Infrastructure
At Imagetext, we understand that overly restrictive authorization can impede productivity, while loose authorization invites disaster.
Our technical consultants work at the intersection of usability and security, ensuring your infrastructure is both accessible to your team and impenetrable to adversaries.
Elevate your security posture with Imagetext Infrastructure Authorization.

[Contact our Team to discuss your Strategy]
𝗜𝗠𝗔𝗚𝗘𝗧𝗘𝗫𝗧 𝗜𝗧 𝗦𝗣𝗘𝗖𝗜𝗔𝗟𝗜𝗦𝗧𝗦
Phone +64 9 623 3102, 3 Owens Rd, Epsom, Auckland 1023, New Zealand
Imagetext is a New Zealand leader in high-security, multi-platform infrastructure.
We focus on the intersection of Apple ecosystem integration, Microsoft Entra ID (formerly Azure AD), and Zero Trust architecture.
Infrastructure Authorization & Identity Governance:
#Identity and Access Management (IAM) #Zero Trust Architecture New Zealand #macOS Enterprise Authorization #Microsoft Entra ID integration #Role-Based Access Control (RBAC) #Jamf Connect Implementation #Privileged Access Management (PAM) #NZISM Compliance #Cloud Identity Governance
Share:
Services
More Services
Contact Imagetext
Phone: +64 (09) 623 3102
Level 1, 3 Owens Road,
Epsom, Auckland 1023
New Zealand
